Reclaim Group Policy Preferences for Microsoft Intune
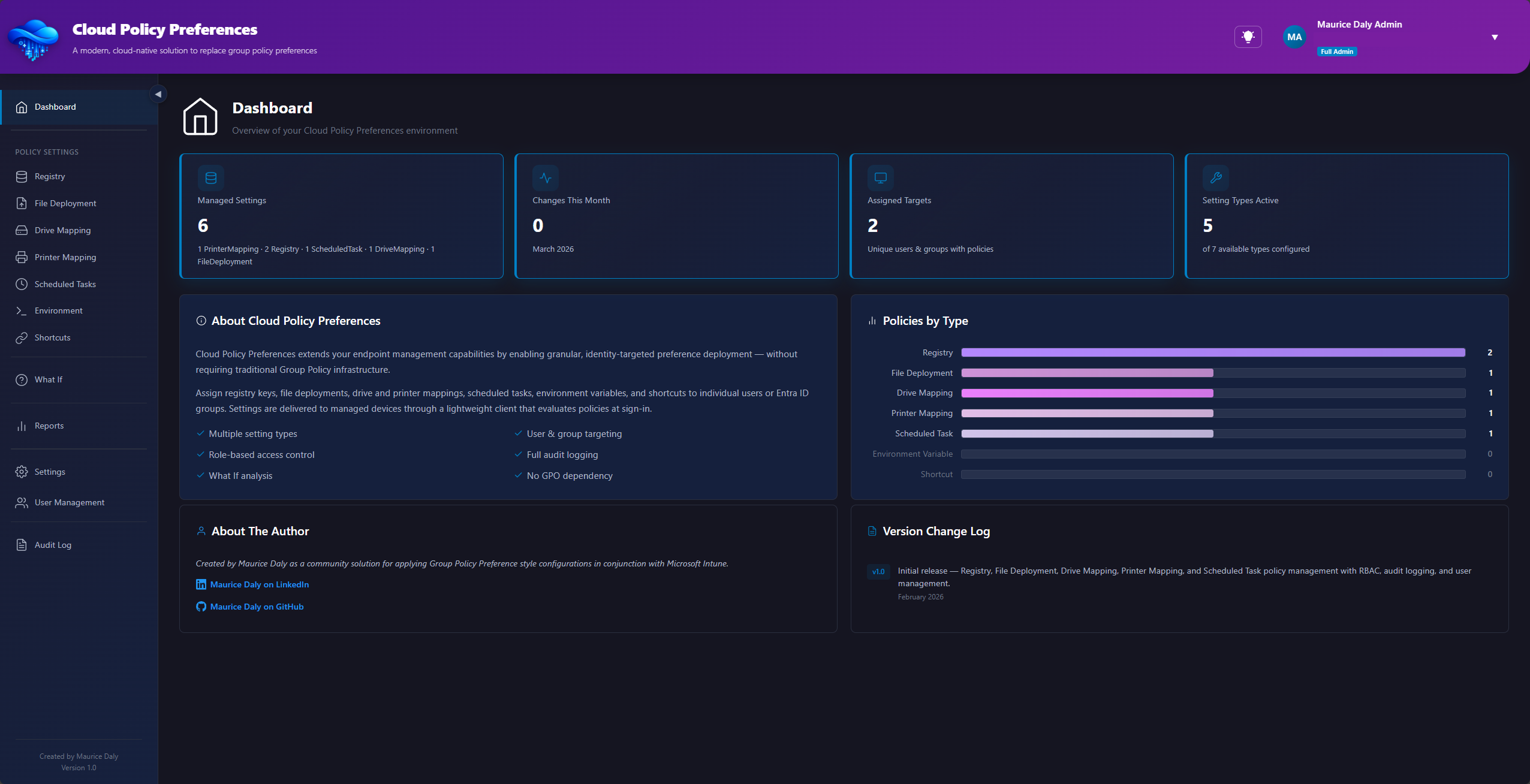
Free Community ToolA modern, cloud-native SaaS platform that brings back registry settings, drive mappings, printer configurations, file deployments, and more — with enterprise-grade security, RBAC, and reporting built in.
Everything you need to manage endpoint preferences
A comprehensive toolkit designed specifically for Intune administrators who need the granular control that Group Policy Preferences once provided.
Policy Deployment
Deploy registry, file, drive, printer, shortcut, scheduled task, and environment variable policies with real-time monitoring and granular scope-tag targeting.
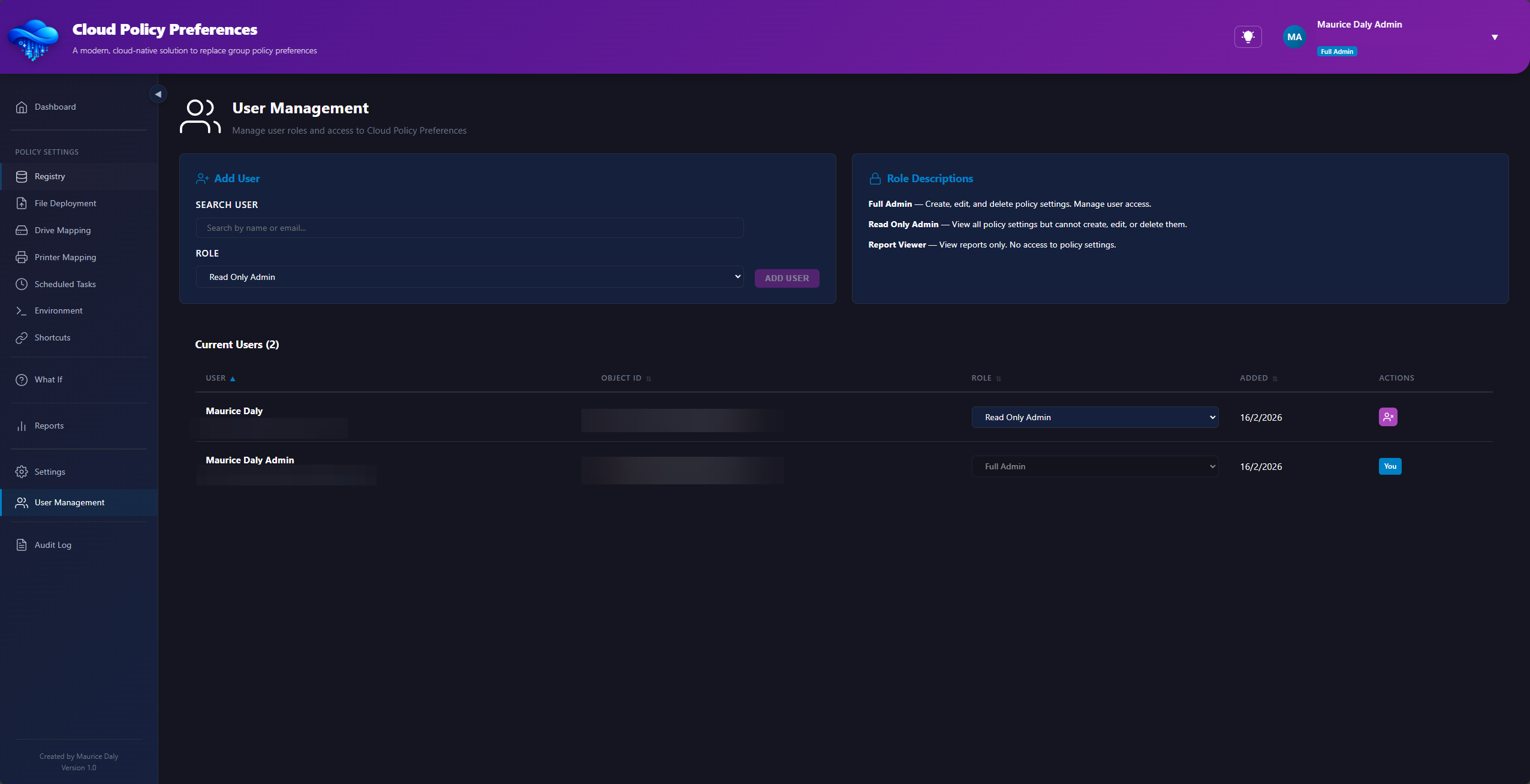
Role-Based Access Control
Define custom roles with granular permissions. Scope assignments to specific users or groups, and enforce least-privilege access across all administrative functions.
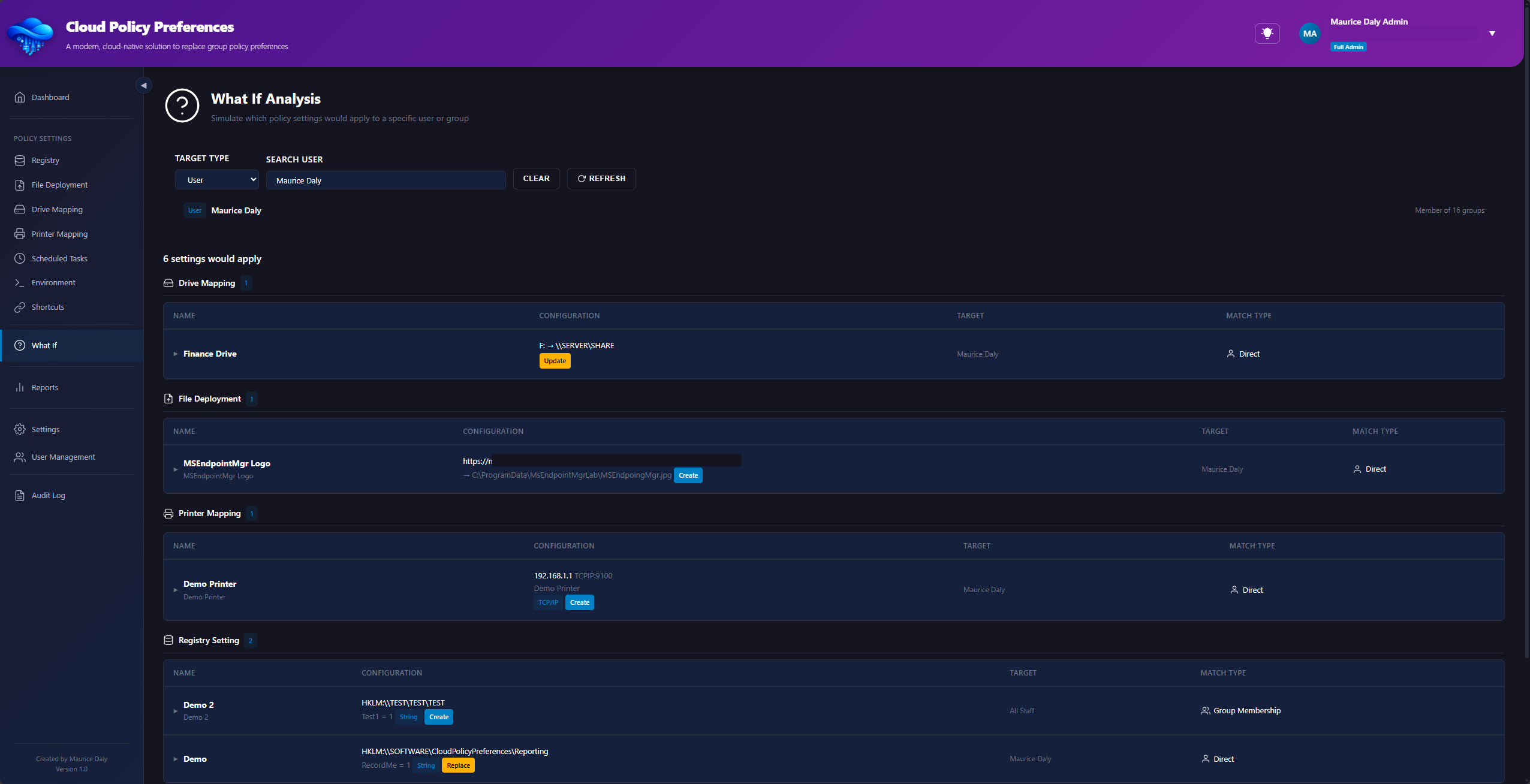
What-If Analysis
Preview which policies apply to any user, device, or group before making changes. Spot conflicts and overlapping assignments in seconds.
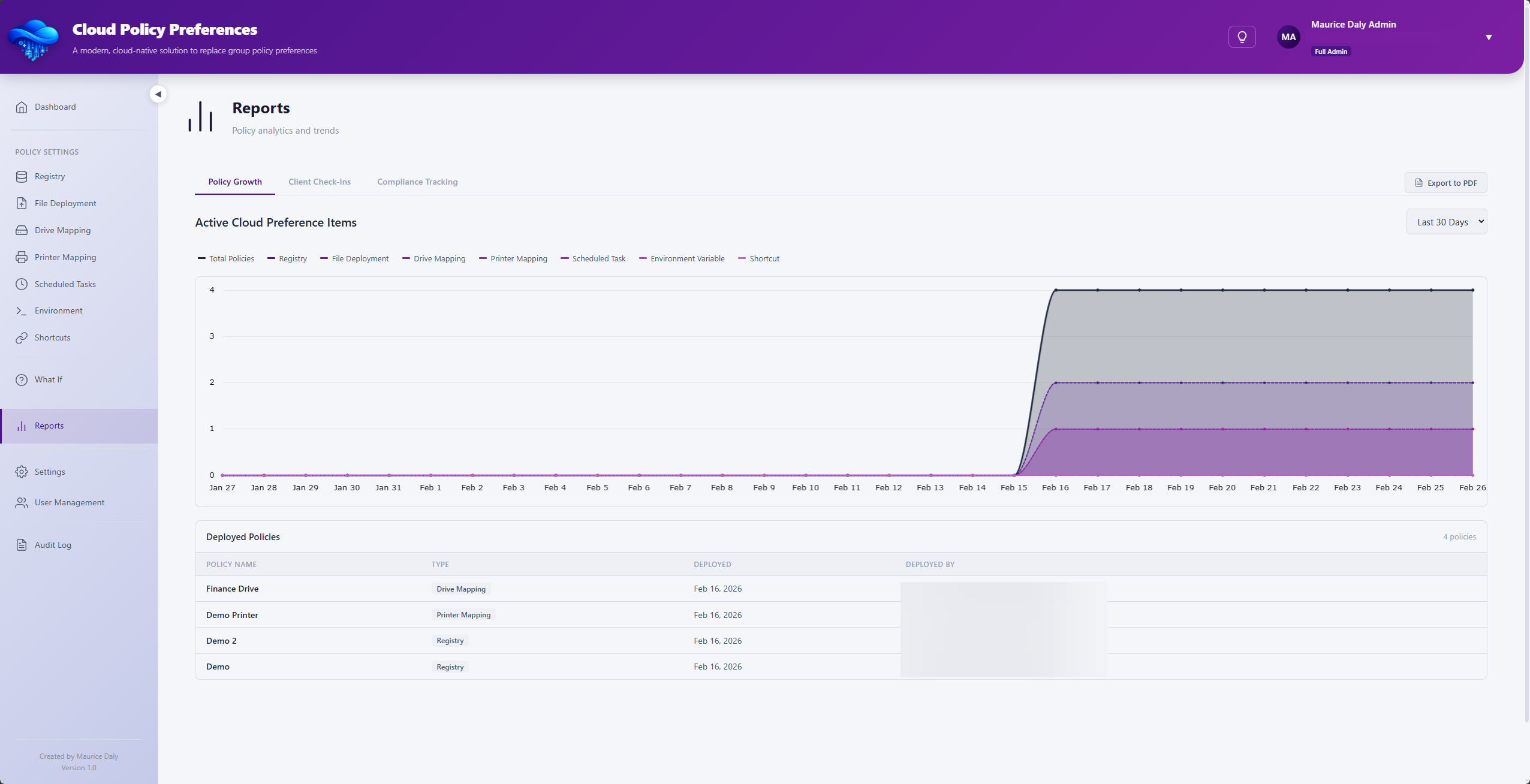
Reporting & Auditing
Export detailed PDF reports, monitor settings drift, track client check-ins, and get at-a-glance dashboard insights across your entire fleet.
File Validation
Automated 5-minute validation scans for PowerShell scripts and shortcuts. Blocked policies are quarantined until validation passes — keeping your fleet safe.
Teams Notifications
Receive daily Teams webhook notifications for policy changes, validation alerts, and client check-in summaries — keeping your team informed automatically.
Seven policy types — one unified platform
All the preference types you relied on in Group Policy, now managed from the cloud through a single, intuitive interface.
Enterprise-grade security at every layer
From data at rest to data in transit, every aspect of Cloud Policy Preferences is designed with zero-trust principles and multi-tenant isolation.
TDEK — Per-Tenant Encryption
Each tenant generates their own Tenant Data Encryption Key (TDEK) — a 256-bit AES-GCM key stored securely in Azure Key Vault. The TDEK encrypts sensitive operational data such as device identifiers and user information, ensuring complete tenant isolation.
- AES-256-GCM encryption with unique IV per field — no two ciphertexts are identical
- HMAC-SHA256 pseudonymisation for partition and row keys prevents plaintext identification of tenants, devices, or users in storage
- Key Vault-backed storage with managed identity access — keys are not exposed to application code or configuration
- Built-in key rotation: generate a new TDEK and all existing encrypted records are automatically re-encrypted with zero downtime
- Tenant-exclusive — each organisation's key is isolated, ensuring one tenant's TDEK is unable to decrypt another tenant's data
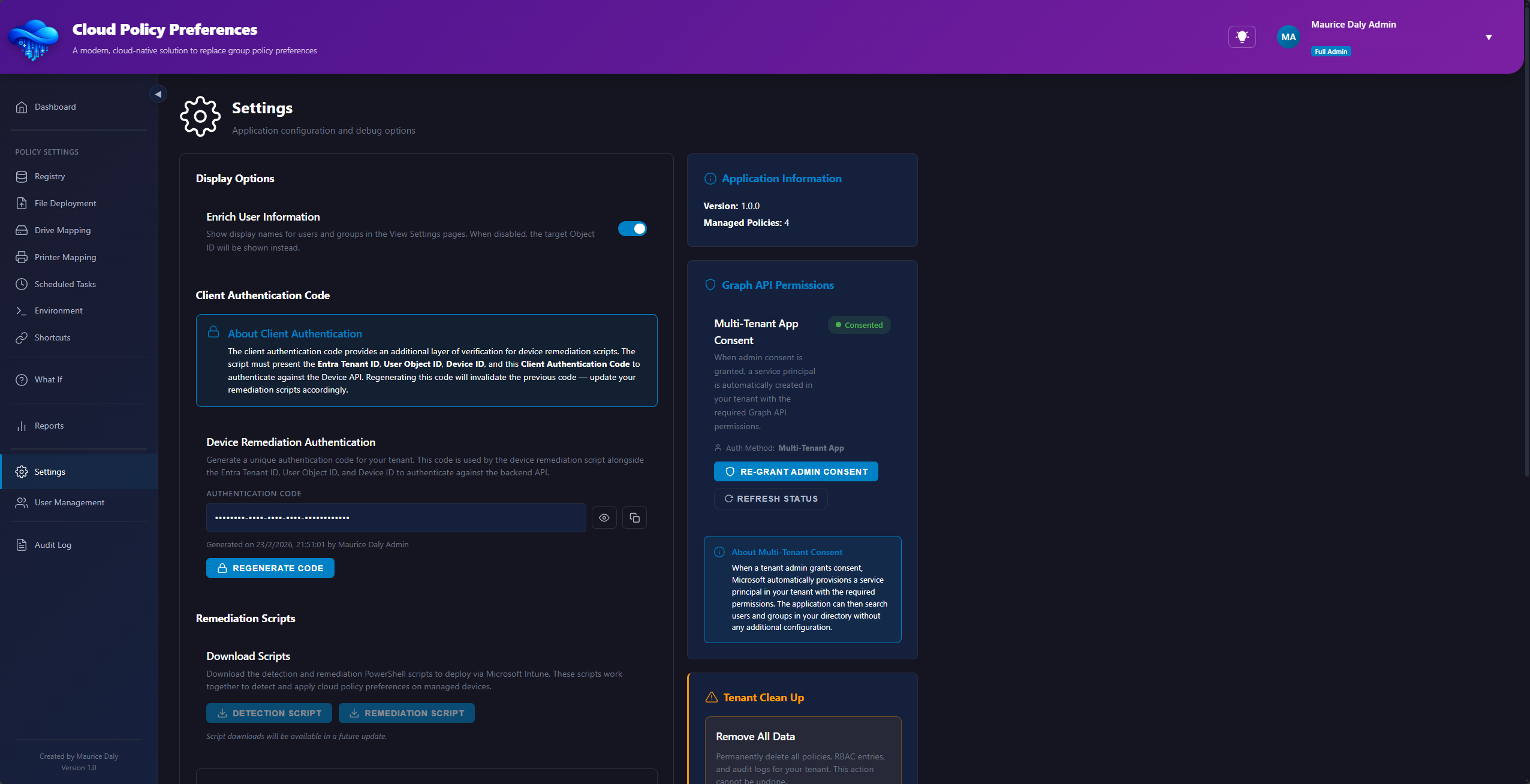
API Key — Device-to-Cloud Trust
Every device-to-cloud API call is authenticated with a per-tenant API key, ensuring only authorised endpoints in your organisation can retrieve policy payloads. The key is generated by the admin and can be rotated at any time.
- Cryptographically random API keys generated via the admin portal
- Transmitted as a bearer token over HTTPS — validated server-side on every request
- Scoped per tenant: a key from Tenant A cannot access Tenant B's policies
- Instant revocation with ability to regenerate a new key if compromised
- Combined with Entra ID Managed Identity authentication on the function app for defence-in-depth
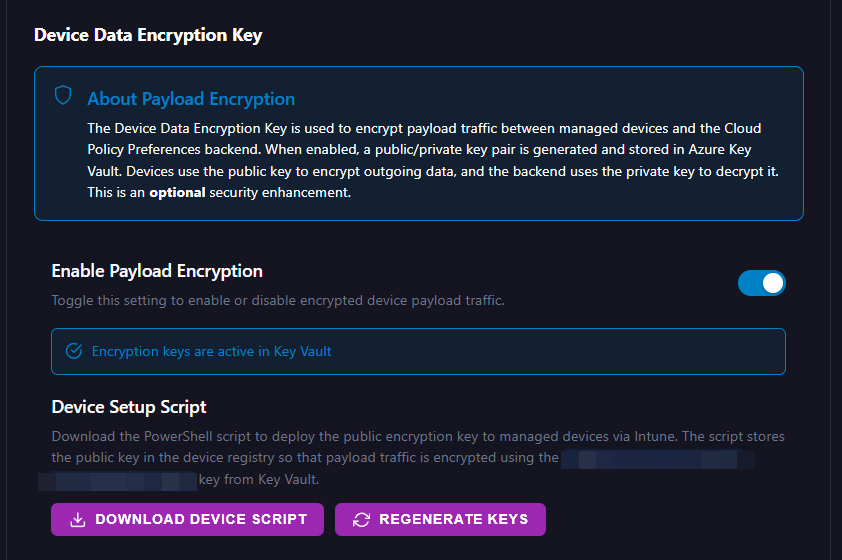
Payload Encryption — In Transit & At Rest
Policy payloads delivered to devices are encrypted end-to-end. Data stored in Azure Table Storage is protected by the tenant's TDEK at the field level, and all API communication is enforced over TLS 1.2+.
- Field-level AES-256-GCM encryption for sensitive properties (names, descriptions, user identifiers, targeting data) stored in Azure Table Storage
- TLS 1.2 enforced on all API endpoints — plaintext HTTP is not accepted
- Azure Front Door provides DDoS protection, WAF rules, and global HTTPS termination
- Policy content is transferred compressed and encrypted; only the client device with the correct API key context can consume the response
- Audit log entries capture who changed what and when — all access is auditable
Entra ID Authentication & Least Privilege
All administrator access flows through Microsoft Entra ID with conditional access support. The platform requests only the minimum Graph API permissions required — read-only access to directory data — so you stay in control.
- Entra ID authentication for every admin session — no local accounts
- Conditional access compatible — enforce MFA, compliant devices, and named locations
- Only read-only Microsoft Graph scopes requested — no write permissions to your tenant directory
- Managed Identity for all Azure-to-Azure communication (Storage, Key Vault) — no stored credentials
Tenant Isolation by Design
Every data query is scoped to the authenticated tenant's ID. Partition keys in Azure Table Storage are prefixed with the tenant identifier, so cross-tenant data access is prevented at the architecture level.
- Tenant ID decoded from the Entra ID token on every request — not supplied by the client
- All storage queries filtered by
PartitionKey eq '{tenantId}_...' - HMAC-pseudonymised keys mean even raw storage access reveals nothing about tenant identity
- Separate TDEK per tenant — encryption keys are not shared across organisations
Multi-Admin Approval
Enforce a four-eyes principle for sensitive policy changes. When multi-admin approval is enabled, create, update, and delete operations require sign-off from a second administrator before taking effect — preventing accidental or unauthorised changes from reaching your fleet.
- Per-tenant opt-in — enable multi-admin approval from the Settings page with a single toggle
- Self-approval prevention — the admin who requests a change cannot approve their own request
- Policies remain in a Pending state until approved; blocked policies are excluded from device payloads
- Full audit trail — every approval and rejection is recorded with the approver's identity and timestamp
- Admin notification on sign-in — pending approvals are surfaced automatically so nothing is missed
Azure OpenAI Script Validation
Every PowerShell script and shortcut target uploaded to the platform is automatically analysed by Azure OpenAI (GPT-4o-mini) for malicious patterns, obfuscation techniques, and MITRE ATT&CK indicators — adding an intelligent safety layer on top of static rule scanning.
- AI risk analysis runs automatically alongside static rule validation every 5 minutes — no manual intervention required
- Detects credential harvesting, reverse shells, encoded payloads, obfuscated commands, and data exfiltration patterns
- Each script receives a risk level (Safe, Low, Medium, High, Critical) with a plain-language explanation of the findings
- MITRE ATT&CK technique IDs are mapped automatically for threat intelligence integration
- Threat Detection reports provide trendline charts, approval summaries, and detailed per-script analysis accessible from the Reports page
Up and running in minutes
A simple onboarding flow gets your tenant protected and your policies deploying with minimal effort.
Sign In
Authenticate with your Microsoft Entra ID account. Consent to the minimal read-only Graph permissions required.
Configure Security
Generate your Tenant Data Encryption Key (TDEK) and API key from the admin portal. TDEK is stored in Azure Key Vault automatically.
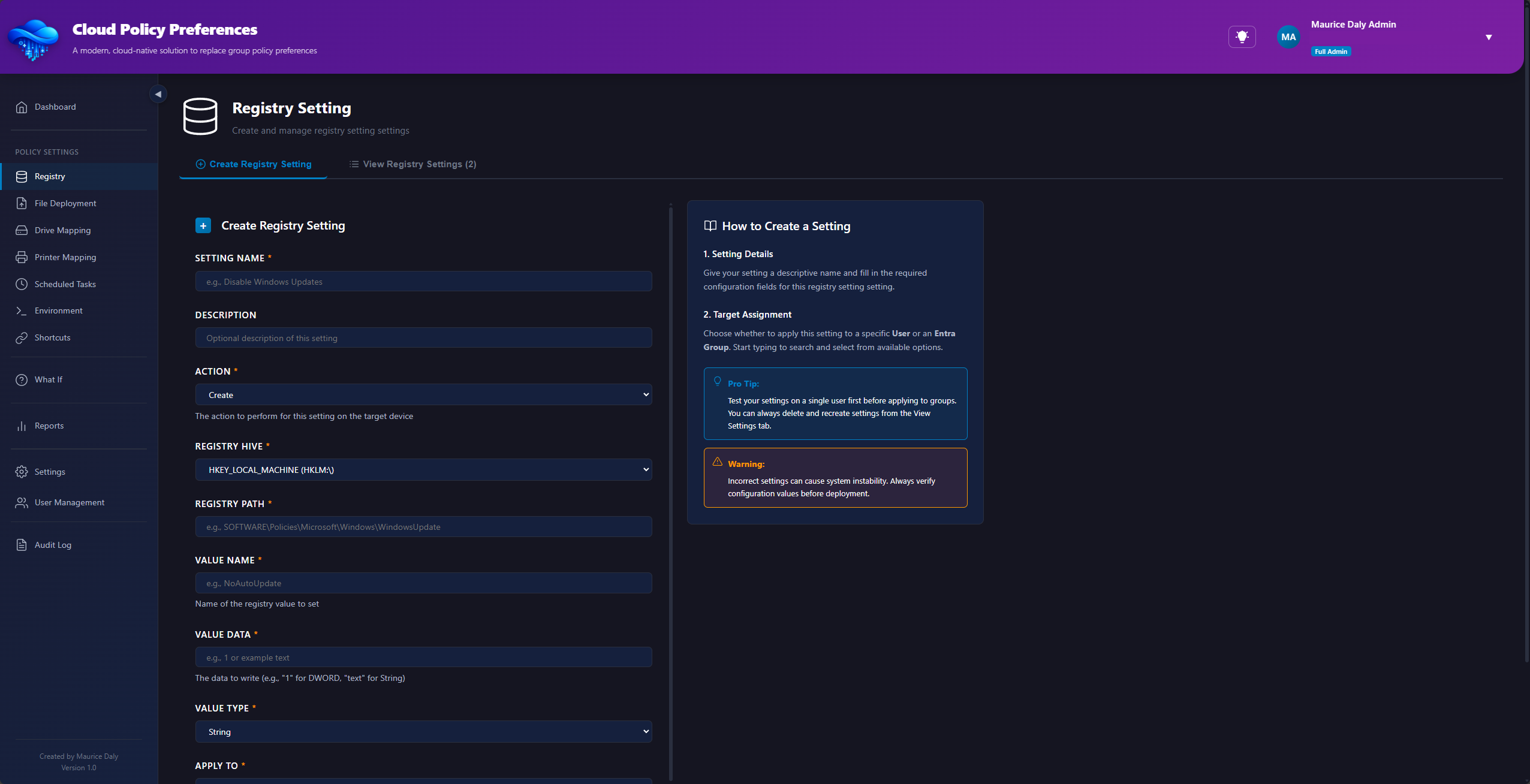
Create Policies
Use the intuitive UI to create registry, drive mapping, printer, file, shortcut, or scheduled task policies with Entra group targeting.
Deploy to Devices
Deploy the lightweight remediation script via Intune. Devices authenticate with your API key and receive their encrypted policy payload automatically.
From sign-in to first policy in minutes
No infrastructure to provision, no agents to build, no complex integrations. Cloud Policy Preferences is designed to get you managing endpoint settings as quickly as possible.
Whether you are migrating from Group Policy Preferences or starting fresh with Intune, the onboarding process is straightforward. Sign in with your existing Microsoft Entra ID account, generate your security keys with a single click, and start building policies using the intuitive web interface.
There is no dedicated server to deploy and no database to configure. The entire platform runs as a managed SaaS service — you focus on your policies while the platform handles the infrastructure, encryption, and delivery.
Get Started NowSign in with Entra ID
Authenticate with your Microsoft account and consent to the minimal read-only permissions.
Generate your security keys
Create your Tenant Data Encryption Key and API key from the settings page — one click each.
Create your first policy
Use the guided policy builder to configure a registry setting, drive mapping, printer, or any supported type.
Deploy to your devices
Push the lightweight remediation script via Intune and devices start receiving their encrypted policy payload automatically.
A modern admin experience
Clean dashboards, intuitive policy builders, and real-time monitoring — all in your browser.
Built on Azure, designed for scale
A serverless, low-cost architecture with enterprise reliability.
Azure Functions
Serverless compute for all API routes, device communication, maintenance tasks, and the admin UI — scales automatically and costs only for what you use.
Azure Table Storage
Cost-effective, high-performance NoSQL storage for policies, RBAC, audit logs, and client check-ins — all tenant-scoped by partition key.
Azure Key Vault
Secure hardware-backed storage for TDEKs, client secrets, and API credentials — accessed exclusively via managed identity.
Azure Front Door
Global load balancing with built-in WAF, DDoS protection, and HTTPS termination — ensuring fast, secure access worldwide.
Ready to modernise your endpoint management?
Launch the admin portal to get started — sign in with your Entra ID account and create your first policy in minutes.
Launch Admin Portal